Social Engineering Targeting SMBs: Tactics, Trends and Simple Defenses
Most small-business breaches don’t start with someone exploiting a zero-day. They start with a polite voicemail, a slightly off invoice, or a text that looks like it’s from FedEx. The attackers aren’t breaking in. They’re being let in.
That’s the premise behind social engineering. Instead of attacking the technology, you attack the person in front of it. It works especially well against small and mid-sized businesses, which tend to hold the data of an enterprise but run with the controls of a household.
What social engineering actually is
Social engineering is when an attacker manipulates a person into doing something that hurts the business: clicking a link, paying a fake invoice, resetting a password for someone they’ve never met, or escorting an unbadged “contractor” into a server room. CISA calls it “the art of human hacking.” Verizon’s annual breach data has shown for over a decade that it features in the majority of incidents that actually cost money.
If you run a small business, the working definition is even simpler. It’s the part of every breach that doesn’t need an exploit. Just a believable story.
Why SMBs are the soft target
The Hiscox 2024 Cyber Readiness Report found that 41% of small businesses experienced a cyberattack in the previous 12 months, up from 38% the year before. The FBI’s 2024 IC3 report logged $2.77 billion in business email compromise (BEC) losses, with a median wire amount around $50,000. Small enough to slip past a one-person finance department, large enough to hurt.
A few reasons SMBs get hit harder than the headlines suggest:
- Same data, thinner defenses. A 25-person dental practice has the same patient PII and ACH credentials as a hospital chain, but no SOC and rarely a CISO.
- Attacks are automated. Phishing kits, lookalike-domain generators, and AI-written spear-phishing copy work at any company size, so attackers don’t pick favorites.
- Decisions are fast and personal. A pretext call to a CFO who already wired $40,000 to that same vendor last month rarely triggers a second sign-off.
The tactics to watch for
1. Phishing and spear-phishing email
Email is still doing most of the work. The 2024 DBIR found the median time for someone to click a phishing link is under 60 seconds, and the median time to type credentials into the spoofed page is under 90. Modern spear-phishing leans on LLMs to mirror your tone, your invoice format, and (when the attacker already has access to a compromised mailbox) your real client list.
2. Business email compromise & vendor email compromise
BEC has been the FBI’s most lucrative cybercrime category for seven years running. The fastest-growing variant for SMBs is vendor email compromise. An attacker hijacks a real supplier’s mailbox, waits for an in-flight invoice thread, and quietly replies with updated banking details. There’s no spoofed domain to spot. The email really is from your vendor.
3. Voice phishing (vishing) and deepfake voice
In 2024, an employee at engineering firm Arup transferred $25 million after a video call with what looked like the company’s CFO. The CFO was a deepfake. Smaller versions of this story show up at SMBs every month: a 30-second voice clone of the owner, lifted from a podcast or webinar, calling the bookkeeper to release a held wire.
4. Smishing and quishing
Text-message phishing (“smishing”) impersonating shipping carriers, payroll providers, and Microsoft 365 password resets has surged. The FTC logged hundreds of millions in losses to text-based scams in 2024. The newer variant is quishing: QR codes embedded in PDFs, parking tickets, or break-room flyers that route to credential-harvesting pages.
5. Help-desk and pretext calls
Several of the biggest breaches of 2023 and 2024 (MGM, Caesars, Clorox, Change Healthcare) started with a phone call to a help desk. The attacker poses as an employee locked out of their account and talks the agent into resetting MFA. The same script works on SMBs whose IT is outsourced to an MSP, often with less verification, not more.
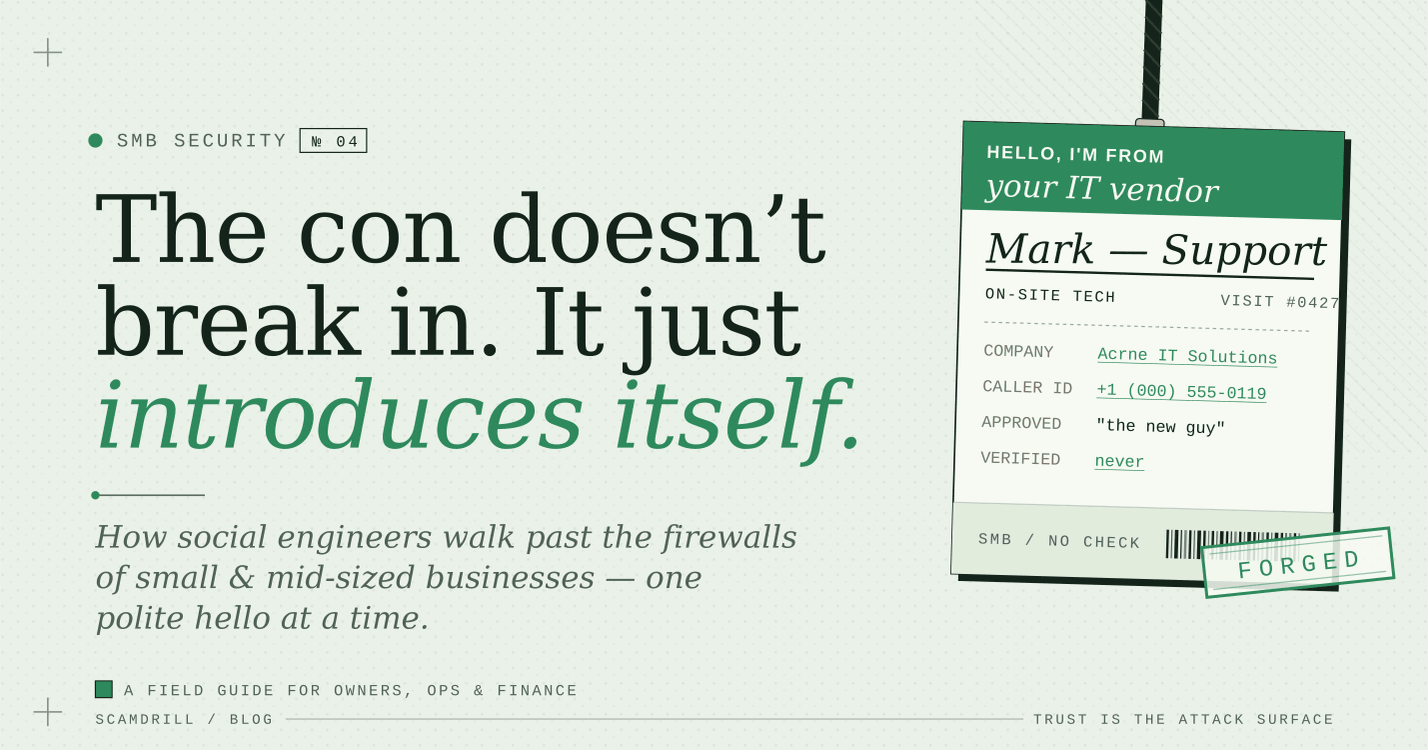
6. Physical pretexting and tailgating
The forged-vendor-badge scenario is not theatrical. CompTIA’s 2024 SMB security survey found that 26% of SMBs had experienced an in-person social-engineering attempt in the previous year. Think the “new MSP technician” nobody scheduled, the fake fire-marshal walk-through, the USB stick dropped in the parking lot.
Red flags shared by every social-engineering attempt
- Manufactured urgency (“this has to be wired today”)
- An authority figure who is conveniently unreachable
- A change to a banking detail, login flow, or contact method
- A request that pre-empts your normal verification process
- Plausible context that’s slightly newer than it should be
What’s new in 2026
AI personalization is now the default. Microsoft’s 2024 Digital Defense Report and CrowdStrike’s 2025 Global Threat Report both flagged generative AI as the biggest accelerant of social-engineering volume and quality. Spelling errors used to be a tell. Now the copy is clean and the tone matches yours.
Deepfake audio and video have gotten cheap. What used to need a Hollywood pipeline now needs a 30-second voice sample and around $20 of cloud time.
MFA fatigue and adversary-in-the-middle (AiTM) phishing. Cisco Talos and Microsoft both report 146% year-over-year growth in AiTM phishing kits through 2024. These kits steal session cookies and walk right past standard SMS or app-based MFA.
Supply-chain pretexting. Attackers increasingly go after the vendor with the weakest controls (your MSP, your payroll provider, your bookkeeper) and use that trusted relationship to pivot into your environment.
Steps you can take this quarter
None of the steps below need enterprise software. Most fit on a one-page policy your team will actually read.
- Require an out-of-band callback for every payment change. Wire instructions, ACH details, and vendor banking updates only get processed after a phone confirmation, using a number from a pre-verified contact list. Not a number in the requesting email.
- Move to phishing-resistant MFA. Replace SMS and app-push MFA on email, banking, and admin systems with passkeys or FIDO2 hardware keys. AiTM kits don’t beat them.
- Publish a no-blame reporting culture. The best predictor of a small breach not becoming a large one is how fast someone reports it. A culture that punishes clickers gets fewer reports, not fewer clicks.
- Run monthly phishing simulations with a 60-second debrief. Annual training has roughly zero impact on click rate. Ongoing simulations cut it by 70 to 90% within a year. See our SMB phishing-training guide for specifics.
- Set a code word for high-stakes voice requests. A shared phrase between owner, CFO, and bookkeeper neutralizes voice-clone wire fraud at near-zero cost.
- Lock down your domain. Enforce DMARC at “reject,” enable SPF and DKIM, and watch for lookalike domains. Your name will be impersonated. Make it hard.
- Train the help desk specifically. A two-page script for verifying password and MFA resets (what to ask, what to refuse) closes the same door that took down half a dozen Fortune 500s last year.
Practice beats policy.
ScamDrill’s organization plans send realistic, current-threat phishing simulations to your team and turn every “oops” into a 60-second teaching moment. When a real attack lands, it lands on a trained inbox.
See the organization plan →What it comes down to
Every breach you’ll read about in 2026 will technically be a phishing problem, a vendor problem, or an MFA problem. Underneath, almost all of them are the same thing: someone trusted a story they shouldn’t have. The defenses aren’t exotic. They’re a callback policy, a passkey, a code word, and a culture that reports small mistakes before they get big.
If you only do one thing this quarter, write the callback policy. If you have time for two, run a phishing simulation. The attackers have already automated their side. Automating yours costs less than the median wire they’re trying to steal.
For deeper rollouts, see our small-business phishing training program and the 30-day simulation rollout plan. For the consumer side of the same playbook (AI voice clones aimed at families), see our AI voice cloning guide.